
A leading Fintech company offers a SaaS product that requires users to have licenses. Previously, they relied on traditional Identity and Access Management (IAM) practices, which involved manual and inconsistent license management. This approach led to issues such as over-provisioning, security risks, and increased operational costs.
TechGrit's technical team, led by seasoned IAM experts, conducted an in-depth analysis of the client's user management challenges. They observed the manual, error-prone processes of traditional IAM and recognized the scalability issues faced by the rapidly growing SaaS company. After extensive research and benchmarking against industry best practices, the team identified SCIM as a superior solution.
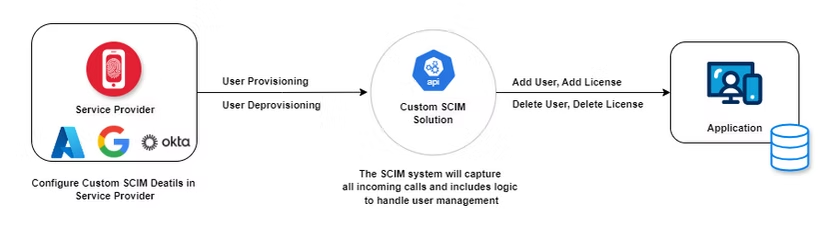
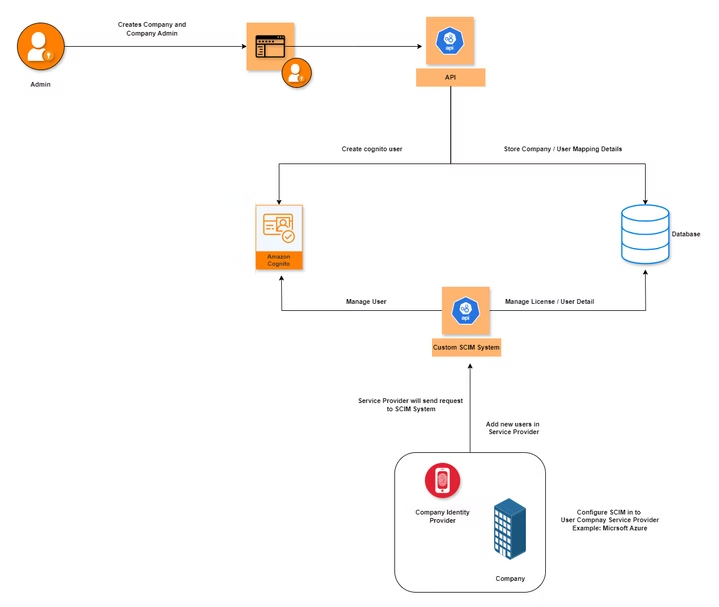
To address these challenges, the company decided to implement the System for Cross-domain Identity Management (SCIM), a standard protocol designed for automating user provisioning and de-provisioning across various identity domains. This implementation would allow their enterprise clients to:
The implementation required building SCIM 2.0-compliant API endpoints within the license management system for managing user resources and licenses:
The default SCIM User schema needed to be extended to include licensing attributes, such as:
entitlements: This field represents the licenses assigned to a user, indicating specific licenses or subscriptions.
The following logic was implemented:
SCIM User attributes (such as userName, active, and entitlements) were mapped to the fields in the license management system.
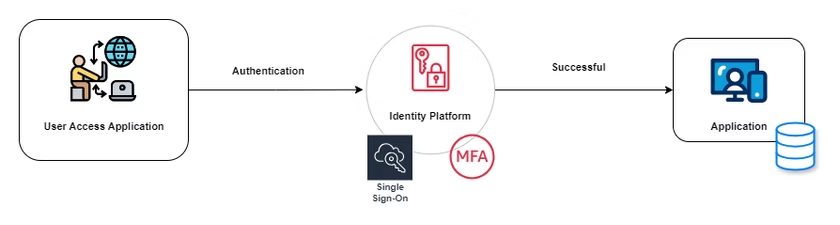
SCIM API endpoints were secured using OAuth 2.0 or Basic Authentication to ensure that only authorized clients could manage their users and licenses.
A synchronization mechanism was developed to facilitate updates between the license management system and the client’s identity provider (IdP). This could involve webhooks, polling, or real-time updates using SCIM events.
The SCIM API adhered to SCIM 2.0 specifications and implemented standard responses for various actions, including:
Mapping the SCIM schema to the application's internal user and group model was initially challenging. SCIM provides a standard schema, but existing user attributes and roles didn't fully align with SCIM's default structure.
Bulk SCIM requests for large organizations could lead to performance bottlenecks.
When syncing with various IdPs, connectivity issues or malformed data often resulted in synchronization errors.
Given that SCIM manages sensitive user data, ensuring the secure exchange of information between IdPs and applications was critical.
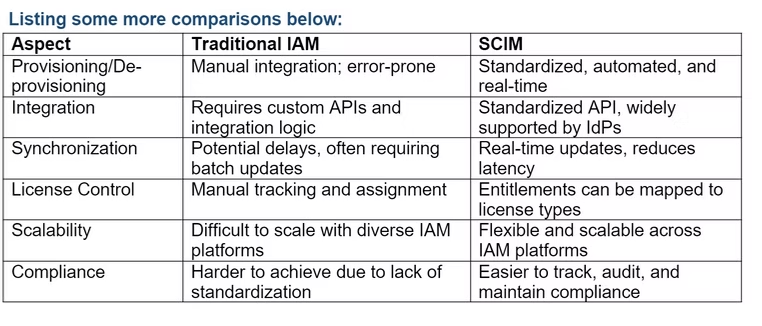
Traditional IAM approaches often require building custom connectors for each IdP, while SCIM provides a standardized schema and protocol, allowing easier integrations.
SCIM automates critical user lifecycle events like onboarding, offboarding, and profile synchronization. In contrast, traditional IAM systems often require manual intervention or custom scripts to manage these workflows.
SCIM is designed to handle large-scale identity synchronization across domains, which is a challenge for traditional IAM systems that aren’t optimized for bulk user operations.
SCIM’s open standard allows it to work across different platforms and identity systems, whereas traditional IAM systems may be more tightly coupled with specific vendor solutions.
Implementing SCIM provided the client with a scalable and automated solution for managing user identities. By leveraging SCIM, they reduced operational complexity, improved security, and enabled seamless integration with customer identity systems. Compared to traditional IAM approaches, SCIM’s standardization and automation make it the preferred choice for modern SaaS applications serving large enterprise customers.